The rate of cybersecurity breaches at large and small companies alike reached alarming levels. With high-profile attacks targeting healthcare, finance, retail, government, manufacturing, and energy, it’s clear that the threat landscape has evolved significantly in recent years.
According to projections, cybercrime is forecast to cost the global economy $10.5 trillion by 2025, reflecting a 15% yearly increase. Businesses have never been more vulnerable; even large enterprises with substantial cybersecurity defenses can fall victim. Lessons learned from these attacks can help smaller businesses prepare their security strategy for any eventuality.
This article discusses some of the most notable company data breaches in 2023 and 2024, their causes, impacts, and what you should do to remain protected.
Recent High-Profile Company Data Breaches
American Express: March 2024
An undisclosed number of American Express customers were notified of a potential breach of their data at the beginning of March 2024. In a statement, American Express announced the incident stemmed from unauthorized access to a third-party merchant processor, rather than their own internal systems.
Customers were informed that their names, account numbers, and card details may have been compromised in the breach, and were urged to monitor their accounts for fraudulent activity over the following 12 to 24 months. American Express users have also been encouraged to enable real-time notifications to alert them to unusual purchases or transactions.
Change Healthcare: March 2024
Change Healthcare was hit by an extensive ransomware attack in February 2024, leading to lasting network interruptions that prevented pharmacies from processing patient prescriptions.
UnitedHealth Group, the parent company of Change Healthcare, announced a “suspected nation-state associated cyber security threat actor had gained access to some of the Change Healthcare information technology systems.” BlackCat has since claimed credit for the attack, stating they accessed 6 TB of data that “relates to all Change Health clients that have sensitive data being processed by the company.”
Early reports suggest the group has been paid a $22 million ransom, though this has not been confirmed by UnitedHealth Group. The far-reaching implications of the attack have gone on to attract federal scrutiny, with the Office for Civil Rights opening an investigation into the breach.
Fujitsu: March 2024
In March 2024, Fujitsu confirmed the presence of malware on its corporate network, which may have left customer information vulnerable to hackers. In its initial statement, the company declined to disclose the number of affected users or the nature of the data that may have been compromised.
Upon discovering the malware, Fujitsu says it “immediately disconnected the affected business computers… Additionally, we are currently continuing to investigate the circumstances surrounding the malware’s intrusion and whether information has been leaked.”
International Monetary Fund: March 2024
The International Monetary Fund (IMF) confirmed a cyber incident was detected in February 2024 in which 11 email accounts were compromised. In a brief statement, the organization said they worked with cybersecurity experts to investigate the breach and re-secure the affected accounts. It concluded:
“The IMF takes prevention of, and defense against, cyber incidents very seriously and, like all organizations, operates under the assumption that cyber incidents will unfortunately occur. The IMF has a robust cybersecurity program in place to respond quickly and effectively to such incidents.”
Roku: March 2024
Roku, a television streaming platform used by 80 million customers, experienced a cyber attack affecting 15,000 account holders early this year. The company claimed hackers had “likely obtained certain usernames and passwords of consumers from third-party sources… It appears likely that the same username/password combinations had been used as login information for such third-party services as well as certain individual Roku accounts.”
The attack highlights the dangers of password reuse across multiple platforms, as Roku customers were locked out of their accounts and attackers attempted to fraudulently purchase streaming subscriptions. Roku assured customers that their social security numbers, full account numbers, and personal information remained uncompromised in the attack, but urged users to reset their accounts and passwords.
U-Haul: February 2024
U-Haul began informing 67,000 customers of a data breach in February 2024, although the data in question is believed to have been compromised in December 2023. Unauthorized access to a reservation tracking system allowed attackers to view US and Canadian customers’ names, dates of birth, and driver’s license numbers. No financial information was accessed, however.
U-Haul stated that legitimate credentials were used to access their system, but they did not reveal how the attackers acquired the login details. The company has since changed customers’ passwords and offered free identity protection services to affected users.
Mother of All Breaches: January 2024
In data security, we encounter not just a breach but a significant data leak, dubbed the “Mother of all Breaches” (MOAB), unveiling a colossal 12 terabytes of information and 26 billion records. Cybersecurity researcher and owner at Security Discovery, Bob Dyachenko, and the Cybernews team discovered this massive compilation includes data from previous breaches and leaks, potentially featuring new, unpublished information.
The leaked data encompasses usernames, passwords, and sensitive information spanning various sources like Tencent, Weibo, Twitter, MySpace, Wattpad, LinkedIn, Adobe, Canva, MyFitnessPal, and government sites like Alabama.gov. Despite some data possibly being outdated, experts stress the substantial risk of credential-stuffing attacks, phishing schemes, and unauthorized account access.
Taking precautions is crucial: individuals should change passwords, enable two-factor authentication, and stay vigilant against phishing attempts. While some data may be from past breaches, regular security upkeep minimizes the need for extensive password updates. Cybernews offers a searchable list of affected sites for reference.
The responsible party remains unknown, underscoring the imperative for enhanced data protection measures and stricter regulations to secure personal information. In the face of such threats, utilizing safety tools and ensuring IT management becomes paramount — consider trying our free IT management platform today!
23andMe: December 2023
DNA testing company 23andMe was subjected to a large-scale breach this year, in which the data of 6.9 million users was leaked. In a statement, the company confirmed that 5.5 million of these users had DNA Relatives enabled, which connects members with similar genetic profiles. A further 1.4 million users had their family trees accessed.
The attack was initiated by a threat actor who employed “credential stuffing” to log into accounts using data leaked in other security breaches. This initial hack provided access to 14,000 accounts, which quickly escalated via the DNA Relatives feature.
23andMe has urged users to reset their passwords and is enforcing a previously optional multi-factor authentication for new and existing users.
Samsung: November 2023
A vulnerability in an unnamed third-party app led to a breach of Samsung customer information in November of this year.
UK-based users who made online purchases in 2020 were affected by the breach, with personal information such as names, phone numbers, emails, and residential addresses accessed in the attack.
TechCrunch reports this is the third data breach at the tech company in the last two years. In September 2022, Samsung issued a notice that its U.S. systems had been subject to an attack. In March of the same year, another breach was confirmed at the hands of Lapsus$ hackers.
Walmart: October 2023
Over 85,000 people were affected by a cyber attack on Walmart this year, with protected health information likely to be among the compromised data.
Walmart issued data breach letters to impacted customers in October and filed a notice of data breach with the U.S. Department of Health and Human Services Office for Civil Rights but has yet to make further details publicly available.
The 2023 cyber attack is the latest in a long history of breaches at the retailer. Most recently, in 2021, a website vulnerability was exploited to access customer information, while a third-party vendor was investigated in 2019 for viewing internal emails without authorization.
MGM Grand: September 2023
In early September, MGM Resorts International experienced a significant cyberattack that disrupted its operations, highlighting the digital vulnerabilities even large corporations face. The attack, attributed to the Scattered Spider group and ransomware by ALPHV (BlackCat), cost MGM an estimated $80 million in revenue over five days. Social engineering played a pivotal role, emphasizing the need for robust cybersecurity measures.
Key takeaways for businesses from the MGM cyber attack include the importance of layered cybersecurity defenses, regular security audits and updates, incident response plans, employee training and awareness, and third-party risk management. Businesses must adopt a comprehensive approach to cybersecurity, as relying on a single security measure is insufficient against modern threats.
Regular audits and updates are vital to staying ahead of evolving threats, while a well-defined incident response plan can mitigate the impact of a breach. Employee training and awareness programs help prevent human errors, and assessing third-party cybersecurity risks is crucial.
Cybersecurity advice for businesses and IT departments from Electric’s Chief Information Security Officer (CISO), Aaron Shierlaw, on getting buy-in for cybersecurity controls: “Keep your leadership informed of current cyber security trends and attacks. Most recently, major Las Vegas casinos were victims of social engineering attacks, which makes an excellent case for investing in better cybersecurity controls.”
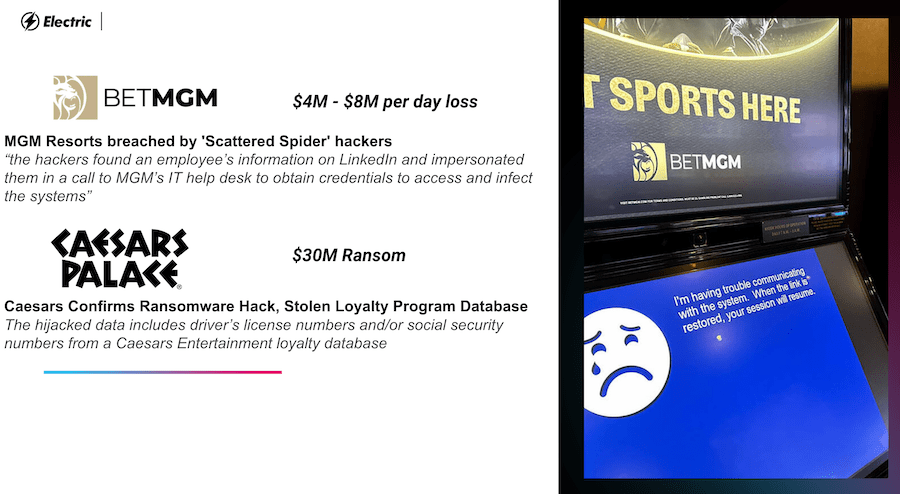
A presentation slide that our CISO used to brief our execs on the MGM and Caesars breaches.
DuoLingo: August 2023
Over 2.5 million DuoLingo users saw their information posted to a hacking forum in August of this year after the data was initially offered for sale in January.
The source of the attack is believed to be an exposed application programming interface (API). Researchers had previously flagged the language learning app’s vulnerability on Twitter (now X), but the security gap remained in place a number of months later.
In a statement, DuoLingo said: “These records were obtained by data scraping public profile information. We have no indication that our systems were compromised. We take data privacy and security seriously and are continuing to investigate this matter to determine if further action is needed to protect our learners.”
PBI & MOVEit: June 2023
The mass hack of file transfer tool, MOVEit, impacted more than 200 organizations and up to 17.5 million individuals as of July 2023. Multiple federal agencies were affected, including the Department of Energy, Department of Agriculture, and Department of Health and Human Services. It’s believed the majority of schools across the U.S were also targeted.
MOVEit is owned by Pension Benefit Information (PBI), a provider of audit, research, and address location services. As the implications of the attack continue to emerge, further breaches have been confirmed at Shell, Siemens Energy, Schneider Electric, First Merchants Bank, City National Bank, and a number of international targets.
Now a far-reaching incident, the attack originated with a security vulnerability in MOVEit’s software. While MOVEit patched the flaw once identified, hackers had already gained access to hordes of sensitive data. Clop, a Russia-linked ransomware group, claims responsibility for the breaches and has threatened to publish stolen information.
Microsoft: May 2023
Microsoft reported that China-based hackers gained access to customer email accounts by forging authentication tokens this year. The attack affected approximately 25 organizations, including government agencies.
An investigation found that Microsoft’s advanced security measures were likely compromised during a system crash in 2021. Sensitive data was briefly moved from a secure production environment to a debugging environment, at which time an engineer’s corporate account was accessed.
As cybersecurity experts, Malwarebytes state, “the attack is a great example of just how advanced and persistent Advanced Persistent Threat (APT) actors can be, and why what Microsoft calls an “‘assume breach mindset” is so important in modern security.”
T-Mobile: May 2023 (and January 2023)
It was announced in May that T-Mobile suffered its second data breach of 2023 after a hack revealed the PINs, full names, and phone numbers of over 800 customers.
This is the company’s ninth data breach since 2018 and second this year. In early January 2023, T-Mobile discovered that a malicious actor gained access to their systems last November and stole personal information – including names, emails, and birthdays – from over 37 million customers. Once they identified the data breach, they were able to track down the source and contain it within a day.
T-Mobile claims they may “incur significant expenses” from this data breach, which will be on top of the $350 million they agreed to pay customers in a settlement related to an August 2021 data breach. Not only has T-Mobile lost hundreds of millions of dollars because of security vulnerabilities, they have also lost customers’ trust after multiple breaches of personal information.
Yum! Brands (KFC, Taco Bell, & Pizza Hut): April 2023
Yum! Brands, the parent company of popular fast food chains KFC, Taco Bell, and Pizza Hut, announced in April of 2023 that a cyber attack had occurred in January. They initially believed the attack only directly affected corporate data. However, out of caution, they are now notifying employees who may have had their data breached.
In a statement provided to Electric, a representative from Yum! says, “In the course of our forensic review and investigation, we identified some personal information belonging to employees was exposed during the January 2023 cybersecurity incident. We are in the process of sending individual notifications and are offering complimentary monitoring and protection services. We have no indication that customer information was impacted.”
The attack resulted in the company closing down almost 300 locations in the UK in January and has continued to cost the company money in additional security measures, customer communications, and brand perception.
PharMerica: March 2023
Almost 6 million individuals were affected by the large-scale hack of PharMerica earlier this year. One of the leading providers of pharmacy services in the U.S., PharMerica, confirmed sensitive patient information was accessed as part of a wider attack on its parent company, BrightSpring Health Services.
Ransomware group Money Message claimed credit for the attack. Along with personal information, the group accessed patient details such as medications and health insurance information.
In a statement, PharMerica said they are “committed to maintaining the privacy and security of the information entrusted to it. PharMerica has taken, and is taking, additional steps, including changes in its processes and procedures, to help reduce the likelihood of a similar event from happening in the future.”
Discord: March 2023
Discord, the social media and instant messaging platform, suffered a breach this year due to security vulnerabilities at a third-party service provider. When a customer support agent’s account was compromised, hackers were able to access their support ticket queue, customer messages, and user email addresses.
While the attack occurred in March, the incident was not disclosed until May. A small number of customers then waited until August to find out which personally identifying information was impacted.
In a separate attack, Discord.io was also targeted in August 2023. The unaffiliated custom invite service for Discord saw their database breached via a vulnerability in the website’s code. Over 760,000 users were affected in the breach.
Eye4Fraud: March 2023
Eye4Fraud, a provider of fraud protection for ecommerce merchants, was impacted by a significant hack in March of this year. In a statement, the company said a backup file containing limited customer information was accessed:
“We provide fraud protection services for ecommerce merchants, who provide us with limited information about transactions. We do not collect sensitive personal information about individuals like account passwords or full payment card numbers in the course of providing our services.”
However, it’s believed approximately 16 million online shoppers’ accounts were potentially exposed as part of the attack.
ChatGPT: March 2023
ChatGPT has been subject to public discourse because of its revolutionary AI capabilities, but the company faced a setback in late March when they announced a data breach. Officials from OpenAI, ChatGPT’s parent company, said: “In the hours before we took ChatGPT offline on Monday, it was possible for some users to see another active user’s first and last name, email address, payment address, the last four digits (only) of a credit card number, and credit card expiration date. Full credit card numbers were not exposed at any time” (via CMSWire).
The company is handling the aftermath by notifying impacted users, confirming their emails, and adding additional security measures. Many Americans are skeptical of ChatGPT and AI in general, and this data breach is likely to further diminish trust.
Chick-fil-A: March 2023
Popular fast-food joint Chick-fil-A has confirmed a data breach of their mobile app that exposed customers’ personal information. The company noticed unusual login activity, investigated the anomaly, and determined the cyber attack happened within the first few months of 2023. The hacker used email addresses and passwords from a third-party to access the system and acquire data including membership numbers, names, emails, addresses, and more.
Although less than 2% of customer data was breached, Chick-fil-A is already taking measures to prevent future cyber attacks. The restaurant announced they would increase online security and monitoring and also reimburse any accounts that suffered from the attack. If you think your account was affected, here is how you can secure your account and get reimbursed for any unauthorized transactions.
NCB Management Services: February 2023
NCB Management Services, a debt collection company, experienced a system compromise earlier this year that resulted in the exposure of masses of financial data. Over 1 million people were believed to be affected by the hack across a number of associated financial institutions.
Bank of America account holders were among the first to be notified that their personal information had been stolen, including addresses, phone numbers, email addresses, birth dates, and Social Security numbers. Credit card and account numbers were also accessed. A short time later, Capital One also confirmed 16,500 of their customers were impacted by the breach.
Unconfirmed reports suggest NCB paid a ransom to the attackers, after the company filed breach notification letters stating they had “obtained assurances that the unauthorized third party no longer has access to any of NCB’s data”.
Activision: February 2023
The video game publisher behind the Call of Duty franchise, Activision, confirmed on February 19th that they had suffered a data breach in December. The hacker used an SMS phishing attack on an HR employee to gain access to employee data, including their emails, cell phone numbers, salaries, and work locations.
Activision claims that the attack was addressed swiftly, and the hackers didn’t obtain sufficient data to warrant alerting their employees directly after the data breach. However, a security research group investigated the breach and reported that the hacker had also gained access to the gaming company’s 2023 release schedule, along with sensitive employee info. Under California law, if 500 or more employees’ data is breached, the company must alert those affected.
Google Fi: February 2023
Google Fi’s high-profile data breach comes as a consequence of the T-Mobile data breach earlier in 2023 (discussed above). Because Google doesn’t have its network infrastructure, they piggyback on T-Mobile’s network and were affected by their massive data breach, compromising their customers’ phone numbers.
Even with just stolen phone numbers, cybercriminals can continue to wreak havoc, especially through smishing attacks that trick users into clicking dangerous SMS links. If you are a Google Fi user, be extra careful of suspicious messages in 2023.
Verizon: January 2023
Verizon customer details were discovered on an online forum in January of this year, with approximately 7.5 million wireless subscribers affected. The leaked data included the devices, reward systems, and subscription services used by customers, as well as their first names.
The telecom company released a statement clarifying that the material was recirculated data from a previous breach. As with many other incidents on this list, they indicated that the attack originated with a now-terminated third-party vendor.
Despite the fact the leaked data was linked to a past breach, the re-posting of customer data on a new forum highlights the long-term implications of such an attack and the importance of preventing similar incidents.
Twitter: January 2023
Twitter – the social media platform now known as X – suffered a breach connected to users’ email addresses in late 2021. While the issue was identified and fixed in 2022, the email records were published on a hacker forum in the first week of 2023.
Details of 235 million Twitter accounts and the email addresses associated with them were made public in the leak. According to the Washington Post, this posed a particular threat of “exposure, arrest or violence against people who used Twitter to criticize governments or powerful individuals, and it could open up others to extortion.”
Unfortunately, the 2023 incident is the latest in a long history of breaches at the social media giant. In August 2022, Twitter’s former head of security warned of “egregious deficiencies” in the platform’s cybersecurity practices.
MailChimp: January 2023
MailChimp, the email marketing platform, alerted customers to a data breach in January. The incident was the result of a social engineering attack that allowed unauthorized users into an internal customer support tool.
The hackers gained access to employee information and credentials, but the company has since identified and suspended those accounts. In response to the data breach, MailChimp has said: “Our investigation into the matter is ongoing and includes identifying measures to further protect our platform”, according to Bleeping Computer.
This is MailChimp’s first attack of 2023, but they also had data breaches in April and August of 2022. For businesses of all sizes, it’s important to know what to do after a data breach to prevent further attacks in the future.
Norton Life Lock: January 2023
Norton Life Lock notified their customers in mid-January that over 6,000 accounts had been breached in recent weeks due to a “stuffing” attack. Stuffing attacks are when previously compromised passwords are used to hack into accounts that use a shared password, another reason why multi-factor authentication is so important.
Gen Digital, Norton Life Lock’s parent company, sent the notice to accounts they believe could have been compromised and recommended changing passwords and enabling two-factor authentication.
Watch Now: Leadership Series – Post-Data Breach: Navigating a Response Plan
Data breaches in small businesses are on the rise. 61% of SMBs experienced at least one cyber attack in the past year, and 40% endured eight or more hours of downtime as a result. Watch this on-demand webinar to learn how to handle a data breach and establish a response plan.
Companies with the Most Data Breaches in 2023
Some of the most high-profile company data breaches are notorious for their frequency as well as the damage caused.
Facebook is one of the most popular websites in the world today. However, the company has faced numerous privacy issues over the years. Their most recent attack occurred in 2021, affecting 533 million users. Before that, Facebook was also hacked in 2018 and 2014, leaving 2.2 billion and 50 million people impacted, respectively.
Yahoo is another infamous victim of back-to-back cybersecurity incidents. The company was hacked in 2013 and 2014, leaving 1 billion and 500 million people affected, respectively. Their most recent attack in 2017 impacted 32 million users.
Other companies that have experienced repeat data breaches in the recent past include Amazon, Twitter, Microsoft, Uber, AOL, Dropbox, eBay, and more.
Given the high profile coverage of cyber attacks, why do so many companies continue to fall victim to hackers, sometimes on multiple occasions? Here are some of the common causes of data breaches to look out for:
- Old vulnerabilities: It’s not uncommon for a hacker to leave a secret window that they can use to access a company’s systems again after a successful first attempt. Failing to patch these vulnerabilities can lead to a second attack.
- Human error: Employees using weak passwords may expose a company’s systems to subsequent attacks. Other common human errors include employees clicking on malicious links and visiting phishing sites. Unless you perform follow-up security training following an initial breach, employees can repeat previous mistakes that leave your business vulnerable.
- Malware: Hackers use malicious software such as viruses, ransomware, Trojans, spyware, adware, etc., to steal confidential information from an organization’s network system. If a company fails to step up monitoring protocols after its first breach, there is nothing to stop repeat attacks from occurring.
- Weak passwords: Weak passwords or passwords that are re-used on multiple websites leave businesses vulnerable to cyber attack. Password guessing is now a highly automated process that takes hackers a matter of seconds when weak passwords are used.
- Stolen information: As seen in some of the examples above, information stolen in data breaches is often re-used to commit new attacks against fresh targets. Make sure to enforce good password hygiene and multi-factor authentication to minimize the risk of stolen information being used to access your business data.
- Privilege misuse / improper permission management: Businesses should enforce a policy of least privilege when it comes to sensitive information. This approach ensures employees only have access to the data they need to do their job, while confidential information is protected with robust permission management.
- Lost devices: Unencrypted devices are a goldmine of information if they fall into the wrong hands. To avoid cybersecurity breaches as a result of lost or stolen devices, implement a Mobile Device Management solution that allows you to remotely lock and wipe employee devices.
How Common are Data Breaches?
Data breaches are becoming increasingly common. In one recent study – the Verizon 2023 Data Breach Investigations Report – an analysis of data breaches across multiple industries between November 1, 2021 and October 31, 2022 identified:
- 6,248 incidents of denial of service, which disrupt critical business operations
- 3,966 incidents of system intrusion, including ransomware
- 2,091 incidents of lost or stolen assets, such as employee devices
- 1,700 incidents of social engineering attacks, including phishing or pretexting
- 1,404 incidents of basic web application attacks, typically driven by weak passwords and stolen credentials
- 602 incidents of miscellaneous errors, most often resulting from employee mistakes
- 406 incidents of privilege misuse, where employees commit breaches or fraudulent transactions
In total, the report analyzed 16,312 security incidents, of which 5,199 were confirmed data breaches. For businesses of all sizes, this frequency in attacks should be cause for concern – and reason to enforce strong security measures.
Data Breach vs Cyber Attack
Given the interchangeable nature of certain cybersecurity terms, you may be wondering if there is a difference between a data breach and a cyber attack. The key distinction is that not all cyber attacks result in a data breach.
Certain cyber attacks aim to cause business disruption, financial loss, and reputational damage by shutting down key operational systems. However, the majority of cyber attacks aim to steal some form of data – whether personal customer details or financial information. When a cyber attack results in unauthorized access to data, it is considered a data breach.
Data Leak vs Data Breach
Similarly, there is a small but important difference between a data leak and a data breach. In a data breach, sensitive data is accessed without authorization by a hacker or threat actor. In a data leak, confidential data is inadvertently exposed to the public through human error or security vulnerabilities.
How Can Companies Protect Against Hackers?
While the prevalence of cyber attacks is on the rise, there are steps that companies can take to protect their most valuable assets from hackers. Follow these cybersecurity best practices to keep your business safe:
- User access management: ensure you have visibility and control over who has access to your most sensitive data. Only grant employees access to the resources they need to do their job.
- Password management: enforce the use of strong passwords along with multi-factor authentication to prevent unauthorized access to business apps, databases, and confidential resources. Electric’s very own Aaron Shierlaw, CISO, says “to enhance data security and protect sensitive information, implement a policy to limit the usage of third-party applications associated with Google accounts. This proactive measure minimizes potential vulnerabilities and safeguards our systems from unauthorized access or data breaches.”
- Endpoint protection: integrate your solutions for malware detection, network security, and breach prevention for a robust, cohesive security infrastructure.
- Mobile Device Management: an MDM solution keeps your company’s devices secure, no matter where they are used. Remotely roll out patches and upgrades across your entire device inventory, and retain the ability to lock and wipe devices if they are lost or stolen.
- Employee training: employee awareness is key to preventing cyber attacks. Conduct regular training so your teams are equipped to identify suspicious activity, attempted phishing, and other types of social engineering attacks. Aaron Shierlaw, CISO at Electric, says “simulating phishing tests is another good way of keeping your employees on alert. Typically, if they engage with the phishing test, they are required to complete a brief training exercise.“
It doesn’t matter if you’re a small business or a large corporation; in 2023, every modern company is at heightened risk of cyber attack. To keep your data secure, you need a comprehensive cybersecurity solution. At Electric, we help businesses protect their most valuable asset from threat actors. Get in touch to learn more about our unified IT security at the device, application, and network levels.