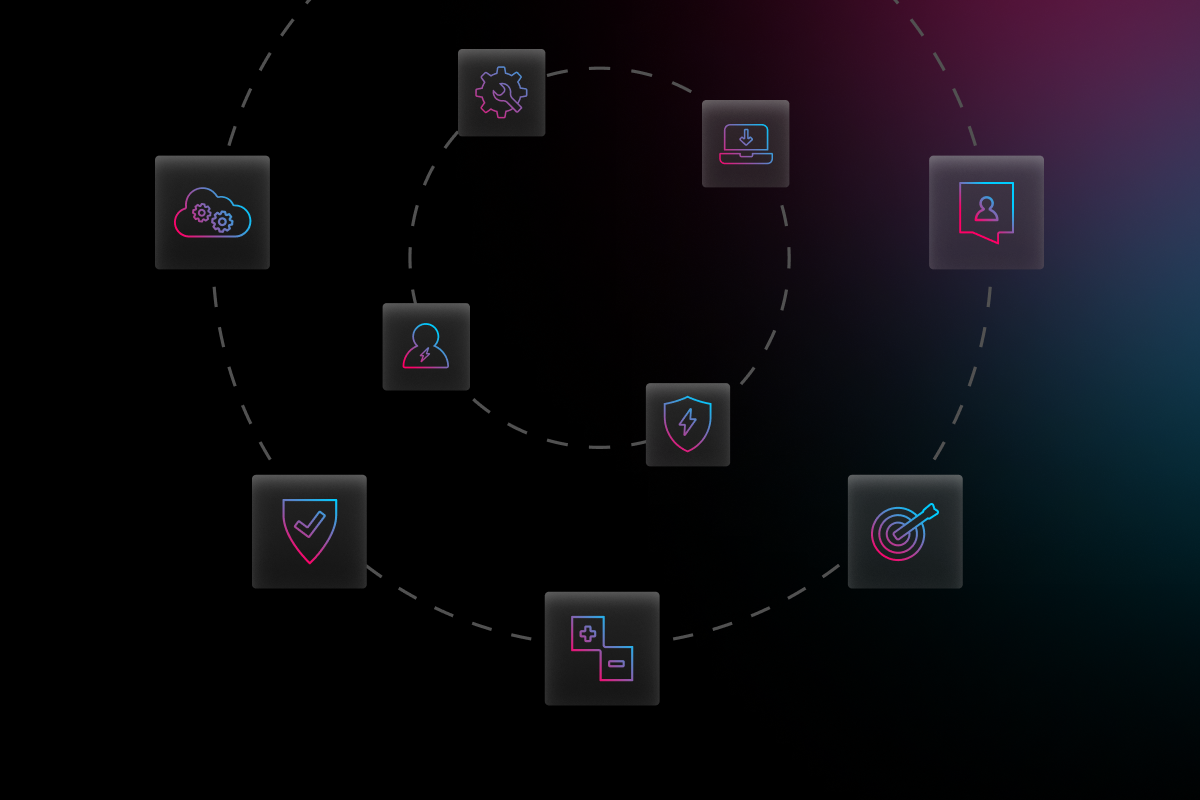
Identity management, or ID management, is a system of many components that helps businesses secure and oversee their user identities and access privileges. Basically, it allows you to know who has access to what while ensuring that information is only being accessed by the right people.
As more businesses move to the cloud and more employees work remotely or off-premises, ID management is more important than ever. Common ID management solutions include effective end user training, single sign on, two or multi-factor authentication, and access management.
The Importance of Identity Management
There was a time when employees worked almost exclusively in the office. This allowed office administrators to have more confidence in who was accessing data because everything was accessed over the company’s network. But now, people have the ability to access their work from almost anywhere outside the office, and on multiple types of devices.
But what happens if a phone or laptop gets stolen, or if an employee’s password is shared with someone who doesn’t work in your company? How is your data and information being protected by outsiders? How do you know that people accessing your data are who they say they are (a superstar)? Nowadays, identity security is just as important as network security, and these issues are the main reason why ID management is crucial for any business.
Components of Identity Management
Better Policies & Training
Implementing and enforcing a password policy is one of the basics of cyber security best practices. According to LastPass, 91% of users know they shouldn’t reuse passwords, yet 61% of them do anyway. How’s that for confidence in your security? Providing regular training and reminding employees of the negative effects of a breach is a vital part of protecting your data. You can deploy a password management system to help create and store complex passwords, making it easier for everyone to “remember” passwords while securing their accounts.
Single Sign On (SSO)
Single sign on (SSO) is one of the simplest forms of password management, allowing users to sign on to multiple services with a single login. Without SSO, users must login to their computers and then login to any type of software or service they need to do their jobs. With the need to remember and use so many passwords, it’s no wonder why so many users reuse the same passwords, even when they know they shouldn’t! But with SSO integration, your system will automatically use an authentication token or ticket to allow access to all your software and services by simply logging into your computer, despite every login having a different password. This means you only need to remember one username and password. While simplifying logins to a single username and password may seem like a security risk, SSO is often used with multi-factor authentication to keep your accounts protected.
Two & Multi-Factor Authentication (2FA & MFA)
Two and multi-factor authentication involves taking more than just one step to sign into an account. The three classic forms of authentications are knowledge, possession, and inherence, and multi factor authentication requires users to prove two out of these three categories when accessing information.
Access Management
The topic of identity management is often paired with access management. While identity management oversees users, roles, and policies, access management enforces them. A user might be able to authenticate their identity when trying to access information, but they won’t be allowed to access that information if they’re unauthorized. Simplifying access to certain data based on a need-to-know basis is yet another way for companies to secure their information and reduce the chances of a breach by unauthorized users.
Need Help?
Any solution you choose for your business should actually solve any issues and problems you’re experiencing. By understanding your organizational needs, you can better implement the right tools and methods needed to keep your data secure. But the truth is, identity management is fairly new in the world of cyber security. Like any technology, it’s also constantly evolving, and there are a variety of solutions out there. Some focus on one or two components better than others, so it’s important to find the one that’s right for you.
Figuring out all your bases to cover is not an easy process to navigate, and that’s why Electric is here to support your SMB. Electric can work closely with your organization to help you find the right solutions to meet the specific needs of your business. Schedule a demo today, and one of our IT specialists will be happy to go over the type of support we can provide for your organization.