Employees like field technicians and sales personnel have worked remotely for years. When they needed access to information stored on office servers, they used virtual private network (VPN) technology. VPNs worked well when there was a limited number of remote workers and digital assets were stored in a central location.
As a result of the pandemic, today’s remote workforce numbers are exceedingly greater. Digital resources are no longer stored locally. Many applications and data are maintained in the cloud for easier collaboration among remote coworkers. Establishing a secure connection for a diversified workforce needs a solution that supports an undefined perimeter. Software-defined perimeter (SDP) technology is a way for organizations to secure an evolving perimeter created by a distributed workforce.
Before we dive into SDPs vs. VPNs, however, let’s define each one.
What is a Software-Defined Perimeter (SDP)?
A Software-defined perimeter (SDP) is a cybersecurity solution that relies on segmentation and user authentication rather than on hardware to create a protective boundary. It is an infrastructure designed to restrict access based on a least-privilege model while allowing administrators to customize and automate security policies.
With SDP technology, individuals are allowed access to the network instead of the application level. Traditional methods granted access according to user privileges. It was based on the applications an employee needed to use. Restrictions were rarely placed at the network level, enabling hackers to move within a network once they could access an application.
SDP solutions authenticate the user and the device. The framework assumes that every connectivity request is suspect and requires verification before access is granted. Once verified at the network level, users are granted access to specific applications and resources based on preset permissions.
How Does SDP Work?
Gaining access with SDP is a two-part process. The user’s identity is verified, and the device’s status is evaluated. Only after passing both protocols is a user granted access to an organization’s digital assets.
Once the user and device are authenticated, SDP solutions create a network connection between the user’s device and the location holding the needed digital resource. The link is specific to the user, device, and help, which minimizes the opportunity for bad actors to take control of the connection. These are the SDP steps for granting a user access to a company’s network.
-
Verify User Identity. SDP solutions typically interface with an identity provider that verifies the user’s identity.
-
Verify Device. SDP evaluates the condition of the device requesting access.
-
Authenticate User and Device. Both user and device are authenticated.
-
Establish Connection. The gateway opens a connection.
-
Enable User Access. End-users can access digital resources based on permissions.
With SDP technology, the perimeter-based verification process is replaced with a secure network connection that does not depend on whether the end-user is inside or outside the trusted network.
What is a Virtual Private Network (VPN)?
A virtual private network (VPN) operates as an encrypted network that runs over an unencrypted network such as the internet. End-users connect to a server using a VPN client. Once the device is authenticated, the user’s device connects to the VPN server, establishing an encrypted “tunnel” for accessing resources inside a trusted network.
In the past, most VPN connections resided on a single VPN server at a company’s office. It was deployed to provide secure communication between a device and network resources. Businesses used VPNs to provide remote technical support of software or enable remote workers to access resources outside the office. Today, VPN services are provided by third parties that offer secure solutions through subscription services.
Once a connection is established, users can access an organization’s network just as they would if they were in the office. Constraints are passed on permissions established at an application level.
SDP vs. VPN
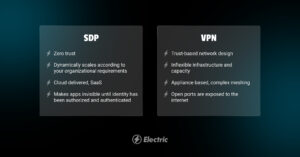
Although both SDPs and VPNs establish encrypted connections between endpoints, how they accomplish those connections is very different. With VPN solutions, users are granted access to all network resources. User connections
are shared. SDP products do not share connections and restrict user access to the specific resources they need.
Managing Connections
User connections in a VPN environment can segment access by deploying multiple VPNs. For example, a VPN could be configured for a marketing department. End users with the proper credentials can establish a VPN connection between their device and the marketing server. A separate configuration can be established for accounting.
Imagine the effort to manage an enterprise-wide VPN implementation that tried to segment users based on the resource being accessed. Not only would there be marketing and accounting VPNs, but there would be VPNs for IT, HR, Development, Product Management, and more. Making a “simple” change could result in catastrophic events, given the complexity of the VPN-based connectivity. To ensure accuracy, testing of each existing connection would be required.
What about the end users? Some employees may need access to multiple VPNs. That could mean that end users would have to sign on and sign off of multiple VPNs. An alternative would be to establish another VPN that allowed access to both marketing and accounting, but the number of connections would soon become unmanageable.
SDPs establish separate connections for each user. There is no VPN tunnel that everyone shares. Because the connections are software-defined, the link is removed when it is no longer needed. IT no longer has to manage a myriad of static connections and open ports, making it easier for IT to see what is happening on the network.
Operating Environments
Unlike VPNs, SDPs are not tied to hardware. They can be deployed on-premise or in the cloud. They can operate in a hybrid or multi-cloud environment. End users can connect from any location, whether it is in the office or at home.
Improving Security
SDPs can be used to create zero-trust networks for added security. In a zero-trust environment, all connection requests are considered to be potential threats. Access is not granted unless the user and device can be verified. SDPs can be used for continuous verification, strengthening network security.
Who SDP Is Better For
Organizations move to an SDP solution when the infrastructure struggles to protect a perimeter-based security solution such as VPN technology. Because SDP provides continuous authentication, IT departments have more visibility of network traffic and activity. Better visibility became crucial as remote traffic grew during the pandemic.
The increase in remote workers resulting from stay-at-home orders also created a security crisis for many companies. With more access points and unsecured home networks, organizations’ attack surfaces expanded, giving hackers more opportunities to identify and exploit vulnerabilities. By deploying SDP, companies developed tighter authentication procedures and more restrictive access to digital resources.
The improved security eliminated known vulnerability targets such as VPNs and Remote Desktop Protocols (RDP). SDP also reduced the opportunities for exploiting cloud vulnerabilities as organizations moved to more cloud-based solutions. Its flexibility made it easier to manage personal devices and home networks used for work.
Who VPN is Better For
For leaner operations, or those not ready to employ the robust security features of a SDP, a traditional VPN might be all you need. While there are many VPN providers available on the market, not all of them are comparable.
It’s important to look for a VPN solution that offers:
-
Robust security
-
Services dedicated to businesses (not consumer grade)
-
Speed and stability
-
Multiple simultaneous connections
-
Easy-to-use apps for different operating systems (Android, iOS, Windows, MacOS, etc)
Leverage Electric to Find the Right Solution
These days there’s so much to consider when it comes to maintaining security for your organization’s data. With many individuals working remotely, it’s important to be mindful of unsecure networks and ensuring the right team members have access to their authorized business systems and applications.
Let Electric’s squadron of seasoned IT professionals guide your team through selecting the proper solutions to protect your sensitive data. Contact us today to learn more.